[ad_1]

Quebec-based supplier of telephony providers VoIP.ms is going through an aggressive Distributed Denial of Service (DDoS) cyber assault, inflicting a disruption in cellphone calls and providers. The incident started round September 16 and has put a pressure on the VoIP supplier’s techniques, web sites, and operations.
VoIP.ms serves over 80,000 prospects throughout 125 nations, lots of whom at the moment are going through points with voice calls.
Voice calls and providers disrupted by DDoS assault
Final week, Canadian voice-over-IP service supplier VoIP.ms announced that it grew to become conscious of a difficulty that was stopping prospects from accessing its web site and was working towards an answer. Quick-forward to right this moment: the problem is ongoing and has been attributed to a persistent DDoS assault.
DDoS is a type of cyber assault wherein a number of computer systems, or “bots,” are concurrently engaged by an attacker to make a lot of requests to an Web server past the server’s capability. As such, an Web server, when going through a complicated DDoS assault, could provide degraded efficiency to prospects, or crash altogether. VoIP is a set of applied sciences that make phone calls attainable through Web-connected servers, which, like every Web service, makes them weak to DDoS assaults.
As of right this moment, VoIP.ms remains to be battling the cyber assault:
All our sources are nonetheless working at stabilizing our web site and voice servers as a result of ongoing DDoS assaults. We perceive the importance of the impression on our purchasers’ operations and wish to reassure you that every one of our efforts are being put into recovering our service.
— VoIP.ms (@voipms) September 22, 2021
As seen by Ars, the VoIP.ms web site is now requiring guests to resolve captchas earlier than letting them in. Previous to this, the web site was throwing HTTP 500 (service unavailable) errors once in a while.
Ax Sharma
As soon as in, the web site states: “a Distributed Denial of Service (DDoS) assault continues to be focused at our Web sites and POP servers. Our workforce is deploying steady efforts to cease this nonetheless the service is being intermittently affected.”
Risk actors demand over $4.2 million in extortion assault
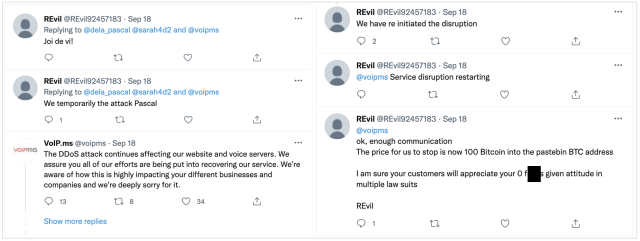
Tweets exchanged between VoIP.ms and the risk actors present fascinating insights. The risk actors behind the DDoS assault go by the title “REvil,” nevertheless it can’t be authoritatively established in the event that they signify the identical REvil ransomware gang that’s identified to have beforehand attacked distinguished firms, together with the world’s largest meat processor, JBS.
Additional, primarily based on the a number of calls for made by the risk actor to VoIP.ms for bitcoins, this incident has been labeled an extortion assault.
“That is presumably a cyber extortion marketing campaign. They create down providers through DDoS after which demand cash. Do not know if the DDoS assault and the ransom demand are from the identical idiots,” noted Twitter person PremoWeb, pointing to a Pastebin word that has now been eliminated. The eliminated word retrieved by Ars exhibits the attackers’ preliminary ask was for 1 Bitcoin, or slightly over US$42,000:
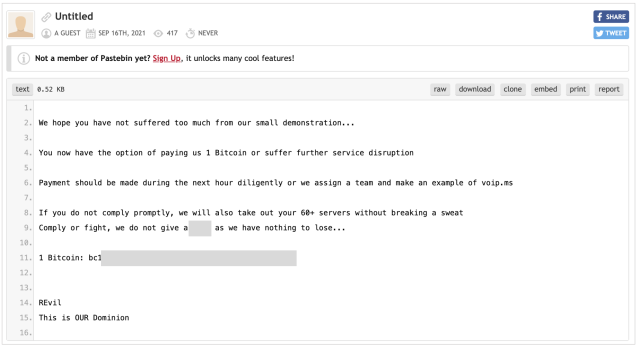
Ax Sharma
However, two days later, the demand was upped to 100 Bitcoins, or over US$4.2 million:
“Okay, sufficient communication… The value for us to cease is now 100 Bitcoin into the pastebin BTC deal with. I’m certain your prospects will admire your 0 [expletive] given angle in a number of regulation fits,” learn the tweet signed “REvil.”
Earlier this month, UK-based telecom VoIP Limitless was slapped with an analogous DDoS assault, suspected to originate from “REvil.” Nevertheless, risk actors behind these assaults are seemingly totally different from the REvil ransomware operator.
“REvil will not be identified for DDoS assaults or publicly demanding ransoms, in a way performed within the VoIP.ms assault,” explains Lawrence Abrams of stories website BleepingComputer. “This assault’s methodology of extortion makes us consider that the risk actors are merely impersonating the ransomware operation to intimidate VoIP.ms additional.”
VoIP.ms prospects can monitor the corporate’s Twitter feed for updates on the state of affairs.
[ad_2]
Source